When Small Problems Cause Big Damage It’s Saturday morning. Your coffee shop is packed, the register is humming, and your baristas are working double-time. Then suddenly — your point-of-sale system freezes. The card reader won’t respond. A line of impatient customers...
Data Protection
When IT Becomes Too Much: How Overburdened SMBs Can Reclaim Time, Security, and Growth
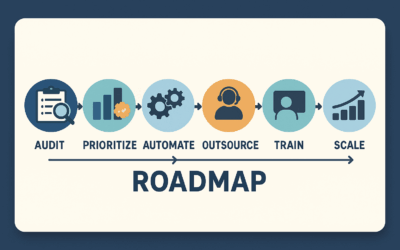
Living in Constant “Break/Fix” Mode If you run a small or mid-sized business, chances are IT has become a daily juggling act. Printers that stall during crunch time. Password resets eating into your team’s productivity. Security patches delayed because you’re “too...
Compliance, Cybersecurity, and IT Resilience: A Guide for Regulated Industries
Why Regulated Industries Can’t Afford IT Mistakes When you run a business in a regulated industry, IT isn’t just about productivity — it’s about survival. A law firm mishandling client data, a healthcare provider with a HIPAA violation, or a financial services firm...
Securing Every Storefront: The IT & Cybersecurity Guide for Multi-Location Retailers
When One Weak Link Hurts the Whole Chain Imagine this: your flagship store is thriving. Checkout lines are smooth, systems are fast, and customers leave happy. But at another branch across town, the POS system is down. Transactions are slow, staff are frustrated, and...
Managed IT & Cybersecurity for Mid-Sized Companies: The Smart Path to Growth
When Growth Outpaces IT Mid-sized companies are in a unique position. You’ve grown beyond the agility of a small startup but haven’t yet reached the scale of enterprise organizations. You’re managing multiple departments, dozens (or hundreds) of employees, remote...
Stop Losing Sales to Printer & POS Problems: The Complete Small Business Survival Guide
When Your Tech Steals Your Sales It’s Saturday morning in Avon, Ohio. Your shop is buzzing, customers are lined up, and this is your busiest time of the week. Suddenly, your receipt printer jams or your POS system freezes. In that moment, all the effort you put into...
Why SMBs Can’t Afford to Treat Cybersecurity as an Afterthought
If you think your small or mid-sized business is too small to be a target, think again. Cybercriminals don’t discriminate—they automate. Their tools are scanning the internet 24/7, looking for any vulnerable system to exploit. If you’re online, you’re a target. And...
Secure Every Storefront: Cybersecurity Strategies for Retail & Multi-location Businesses
Imagine a busy Saturday afternoon. Your stores are packed with customers, transactions are flowing, and suddenly your payment systems grind to a halt. Within minutes, customers abandon carts, sales plummet, and your brand reputation hangs by a thread. In today's...
Choosing Excellence: Why Great Lakes Computer Trusts SentinelOne to Protect Small & Mid-sized Businesses
Imagine waking up to an urgent alert: Your business’s critical systems have been breached, and your entire customer database is compromised. For small and mid-sized businesses (SMBs), cyberattacks aren't just IT problems—they’re potentially business-ending events....
Defending Your Registers: Cybersecurity Essentials for Retail & Multi-location Businesses
Picture your busiest shopping weekend of the year. Suddenly, your payment terminals freeze, customers abandon their carts, and frustrated shoppers head elsewhere. For retail businesses, especially those operating multiple locations, cybersecurity isn’t just a tech...