Data Security
IT Business
Your Trusted Cybersecurity and Data Protection Partner

Data Protection and Privacy
Data Security
Weak Links In Your Cyber Security
The Great Lakes Computer
Data Protection and Security
Data security is the process of safeguarding digital information throughout its entire life cycle to protect it from corruption, theft, or unauthorized access.

Data Backup and Recovery Services for Uninterrupted Business Continuity
At Great Lakes Computer, we provide a variety of data backup and recovery options to cater to your specific requirements.
Discover our enterprise-level backup and recovery solution, Unitrends from Kaseya, which offers robust features at an affordable price for small and medium-sized businesses. Additionally, we are proud partners and resellers of Asigra Cloud Backup, a comprehensive agentless backup and recovery software platform trusted by organizations worldwide.

Enhance Security with Security Operations Center as a Service (SOCaaS)
In the modern threat landscape, a Security Operations Center (SOC) is crucial for comprehensive security.
Regardless of the size of your business, data breaches can pose significant risks. In fact, more than 70% of ransomware attacks target small businesses. At Great Lakes Computer, we believe that every organization deserves top-level protection, which is why we offer Security Operations Center as a Service (SOCaaS). By leveraging the cloud and an as-a-service model, we make advanced security more accessible and affordable for businesses of all sizes.

Comprehensive Cybersecurity and Compliance Solutions
Don’t leave your business vulnerable to hackers and regulatory compliance issues. Great Lakes Computer offers a comprehensive suite of cybersecurity and compliance services to fortify your defenses. Our approach extends beyond simple firewall and antivirus solutions. We conduct regular testing of technical controls, review and update written policies, and provide user training to ensure safe interactions with systems and data. Our goal is to empower your organization with robust security measures and proactive risk management.

Secure Your Email Communications with Mimecast
Email remains one of the most common attack vectors for cybercriminals. Protect your organization’s email infrastructure and bolster cyber resilience with Mimecast. As a leading cybersecurity provider, Mimecast enables thousands of organizations worldwide to implement comprehensive email security strategies. From safeguarding against threats to archiving and data protection, Mimecast offers a powerful suite of cloud-based solutions. With Mimecast, you can restore trust in your email communications while mitigating the risks posed by cyberattacks, human error, and technical failures.
Next-Generation Endpoint Protection Platform
Traditional antivirus and firewalls are no longer enough to combat advanced threats. Upgrade your network defense with the SentinelOne Endpoint Protection Platform. Powered by machine learning and automation, this unified solution combines prevention, detection, and response capabilities in a single purpose-built agent. With rapid threat elimination, policy-driven response automation, and real-time forensics, SentinelOne provides complete visibility into your endpoint environment. Strengthen your network security and stay ahead of emerging threats with SentinelOne.

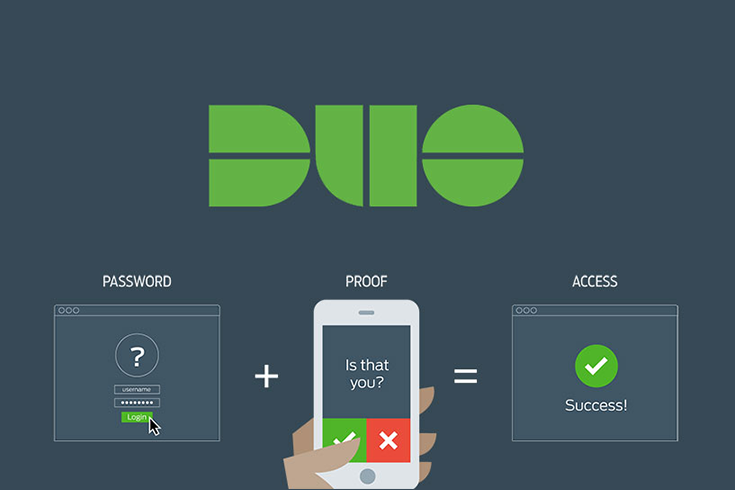
Introducing DUO Two-Factor Authentication for Enhanced Security
Great Lakes Computer is excited to introduce our new partner, Duo, and their innovative two-factor authentication solution. With DUO, you can enjoy the perfect balance of security and convenience. By implementing two-factor authentication (2FA), you create an additional layer of protection against unauthorized access to your applications and environments. Verify the identity of your users easily and effectively, ensuring that only legitimate individuals can access your critical resources.
Get audit-ready with a defensible cybersecurity program, incident reporting workflow, and staff training.