Arctic Wolf Customer,
Arctic Wolf has observed an ongoing phishing campaign in which the device code authentication flow is being exploited to sign in and compromise accounts. Arctic Wolf is actively investigating the campaign, has developed detections, and is alerting customers when this activity is observed. All organizations are strongly recommended to review this security bulletin.
Summary
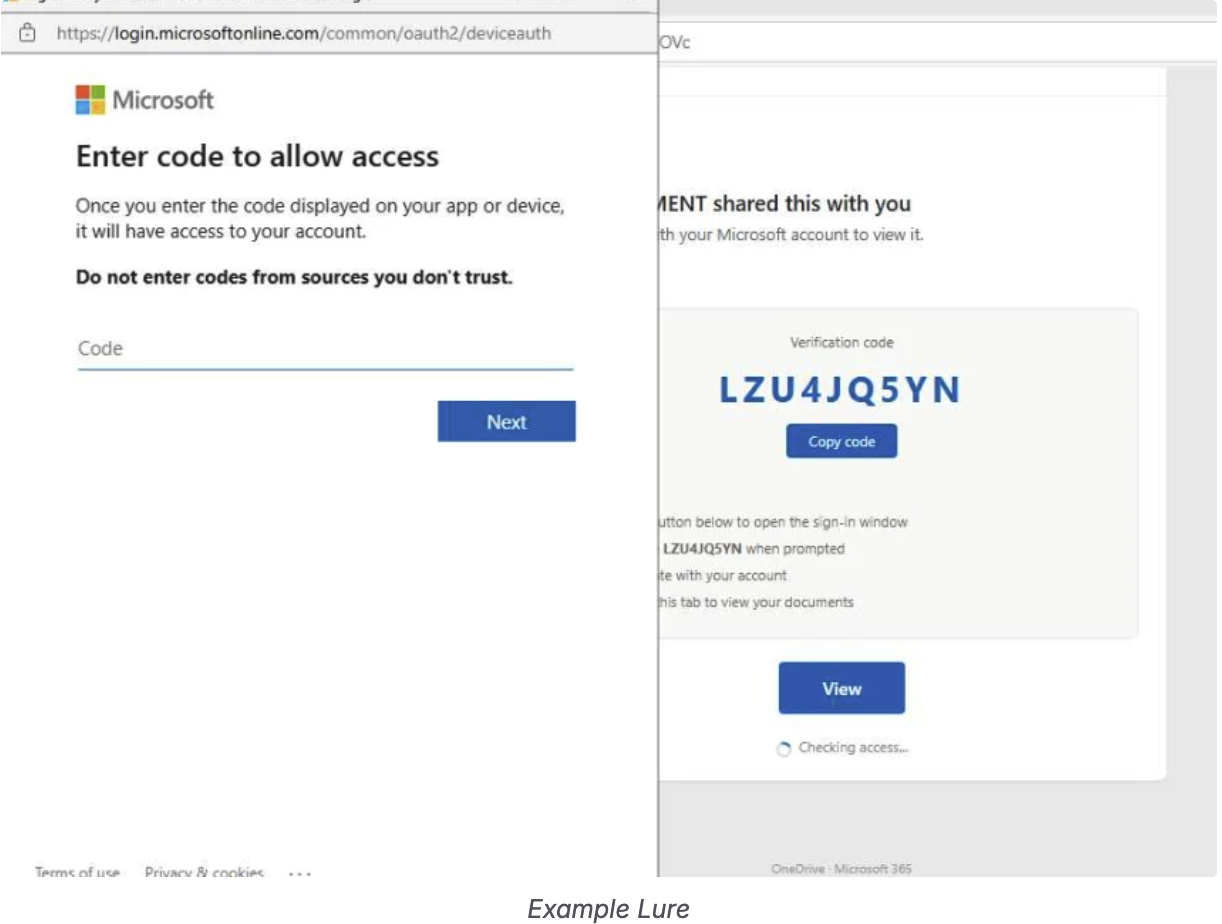
Starting the week of April 12, Arctic Wolf observed a widespread phishing campaign impacting hundreds of customers across multiple regions. A threat actor was observed within customer environments leveraging the device code authentication flow to sign in and compromise accounts. A variety of lures were used in this activity, including DocuSign and Adobe Sign.
This pattern aligns with the EvilTokens phishing-as-a-service (PhaaS) framework, which has been documented as enabling scalable, MFA-resistant credential and token theft. The domains hosting the phishing content, along with device code flow URLs embedded in email chains, were associated with EvilTokens infrastructure.
|
Arctic Wolf has Managed Detection and Response detections in place that apply to activities observed in this campaign, and will continue to notify customers when new instances of this threat are observed.
Arctic Wolf is a customer of its own products/services and so we will follow the same recommendations outlined for our customers in this Security Bulletin.
Recommendation
Block Device Code Flow Where Not Required
Device Code Flow is designed for devices that lack local input capabilities (e.g., smart TVs, IoT devices, conference room displays). However, threat actors increasingly abuse this authentication method in phishing attacks. Arctic Wolf strongly recommends blocking Device Code Flow using Conditional Access (CA) policies where not explicitly required. MDR Customers can request a spot check from their security engineer to identify sign-ins using the Device Code Flow authentication method.
- Create a CA policy targeting “All users” → “All cloud apps” → Conditions: Authentication flows → Device code flow → Block.
If device code flow is required for specific scenarios (e.g., conference room devices), restrict it by:
- Limiting to specific network locations (trusted IPs)
- Limiting to specific device platforms (e.g., Android only for meeting room devices)
- Limiting to specific user groups (service accounts for IoT/signage)
Additionally, enable sign-in risk policies via Microsoft Entra ID Protection to detect anomalous or suspicious sign-ins.
Implement Security Awareness Training
Arctic Wolf strongly recommends implementing comprehensive security awareness training to equip users with the skills needed to quickly identify and report suspicious activity, including the tactics observed in this campaign.
Arctic Wolf offers several phishing-focused modules within its Managed Security Awareness product to help users recognize and respond to the types of threats outlined in this bulletin.
References
- Sekoia EvilTokens Blog: https://blog.sekoia.io/new-widespread-eviltokens-kit-device-code-phishing-as-a-service-part-1/
If you have any additional questions, please reach out to your CST at security@arcticwolf.com.
Thank you,
Arctic Wolf