One of the unvarying truths of the digital world in which all of us–business owners or consumers–operate is that cybercriminals constantly evolve their attacks. This means that the things we used to do for secure access to sensitive account systems like online banking, stock apps, or email accounts have to evolve too. One of these evolutionary methods has been two-factor authentication–also known as TFA or 2FA.
What is Two-Factor Authentication?
Basically, two-factor authentication is an IT tech process by which you need to use two different authentication factors to enter some kind of sensitive digital account. For example, if you want to access your Gmail account, enabling TFA for this would mean having to first type in your password and then also verify that you’re who you say you are by saying yes to a security notification on your smartphone. This is just one basic example of TFA. Variants of it involve verifying with things like:
- Something you have: In this version, you’d then double verify your identity by authorizing access through a special number or notification you receive on your smartphone, a small hardware token or even another email address. You might do this by clicking or agreeing to something in the external device/account, or by receiving a unique number and typing it in on the original device you’re trying to log in from.
- Something you know: In this version of 2FA, you first enter your username/password combination and then are also prompted to hand over some other piece of private information like an answer to a security question, or a PIN number or some kind of additional passphrase. This method doesn’t necessarily require a second device.
- Something that’s part of you: Normally, this version of TFA works through biometrics. In other words, you’re asked to hand over a password or PIN number and then use a retinal scan, fingerprint scan, or biometric face detection to open an account or device. This variant of TFA is often used for accessing devices like advanced smartphones or laptops.
In the case of multi-factor authentication, any combination of the above can apply, but with the inclusion of at least one additional factor that you have to authenticate in some way to access an account or service. An example of this would be accessing something like a cryptocurrency wallet and being asked to type in your password, then verify a notification on your smartphone, and finally being asked to type in a secondary multi-word passphrase.
It’s also worth noting that for the sake of precision, we’re defining two-factor authentication as requiring no more than two factors and MFA as requiring at least three factors in total.
The above versions of TFA essentially cover all of its widely used variants, though they can be implemented in many different ways across many different devices.
Why TFA is So Important
The core importance of TFA lies in its security benefits. If you’re accessing vital accounts through your laptop, desktop, or smartphone and only need your password and username to open them, it’s much, much easier for hackers and cybercriminals to breach these accounts. All they need is that device or in many cases, they just need to guess or spy on your activity to discover the password you use.
Two-factor authentication throws these criminals into a loop by blocking access unless something entirely different is also presented. This is usually something that’s hard to access, like your phone, something you know in your mind, or some part of your physical appearance.
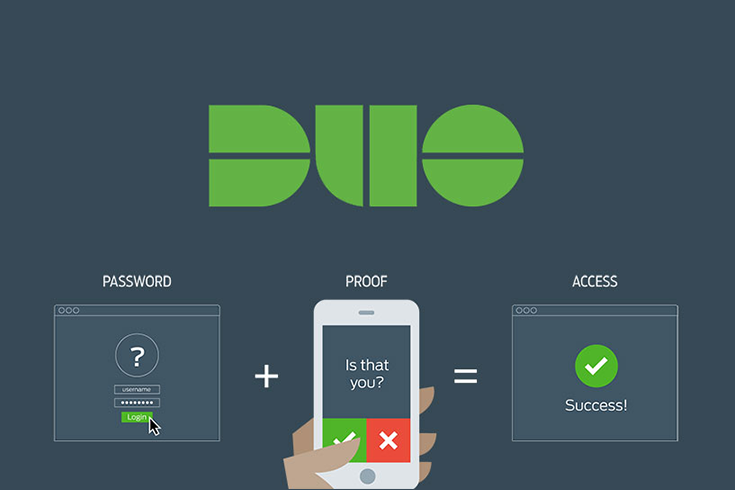
TFA isn’t foolproof though, since no security measure really is. But it makes the work of cybercriminals much more complicated than finding out a single password. At Great Lakes, we are proud to partner with Duo for the 2FA protection we offer our clients. They are one of the best in business when it comes two-factor authentication, protecting our clients’ applications and environments.
How Two-Factor Keeps Evolving
Two-factor authentication has evolved in many ways over time. The methodologies for implementing it that we described above include some of these evolutions.
For example, originally, TFA was often implemented through little special hardware tokens that would give you a unique number to type in any time you tried to access something, like online banking with your password and username. However, because these hardware tokens can be easily lost or broken and are tedious when it comes to delivering them to users, many sensitive digital service providers started implementing smartphone-based TFA.
Since most people increasingly keep their phones on them at all times and even use them to access their accounts, having special passcodes sent directly to these phones has become more convenient.
However, not even phone-based TFA is entirely secure. For this reason, biometric systems and other methods (like multi-factor authentication) have become increasingly common to make account access even more robustly secure and resilient against breaches.
Drawbacks and Weaknesses of 2FA
We mentioned above how one common method of TFA involves verifying account access with your smartphone. Well, a frequent attack against this security technique is called SIM swapping.
Basically, a hacker or cybercriminal contacts your mobile service provider, pretends to be you (or has an inside employee helping them) and swaps your phone’s SIM card authentication over to a phone they own. They can then go to the site of a digital service (such as an online banking service) that you use and pretend to have lost your password, prompting an ID verification to the very SIM card and phone number they’ve just cloned from yours.
This is why TFA systems have been developed which depend on more than two factors or on “un-hackable” things like biometrics. However, even in these cases, breaches can still occur.
How to Protect Your Business Accounts
Unfortunately, there is no 100% foolproof method of guaranteeing a hacker will never access your accounts. However, TFA and its MFA cousin are both much better options than accessing sensitive service through a single password. With any service that offers these security options, you should absolutely apply them.
Great Lakes 2FA partner provides security AND convenience. When you work with GLC and our new partner, DUO, two-factor authentication or multi-identity verification becomes simple for you, yet remains a major roadblock for hackers. Double up on security by protecting your applications and environments with two-factor authentication. It’s the simplest, most effective way to verify that your users are who they say they are.
Expert Tip
Before installing 2FA or any other security measures, be sure to start by uncovering your current vulnerabilities and/or if your credentials are already for sale on the web. Luckily, we have tools to test hack your security measures!
Bob Martin, Owner Great Lakes Computer
Discover if your private info is exposed!