Cybersecurity Compliance Services
Cybersecurity
We offer a comprehensive suite of cybersecurity and compliance services to help businesses combat hackers and meet
regulatory compliance demands.
Being secure means more than just throwing firewall and antivirus at the problem. To be secure, organizations need to regularly test their technical controls, review and update written policies, and ensure their users know how to interact with systems and data safely.
We have partnered with Cyberstone to help us deliver expert knowledge in finding and fixing security problems as well as
helping companies meet PCI, SOX, GLBA, HIPAA, and other regulatory requirements.
helping companies meet PCI, SOX, GLBA, HIPAA, and other regulatory requirements.

Cybersecurity and Compliance Services:
Vulnerability Scanning
We look for areas of weaknesses such as missing patches, outdated firmware, and misconfigured IT equipment. We then provide a prioritized “fix first” remediation report that Great Lakes Computer will address to close gaps in your defenses.
Internal and External Penetration Testing
We look for areas of weakness in the technical environment and then actively attempt to exploit weaknesses. The goal is to answer the question “how easily could a hacker access private data on my systems?”
Web App Penetration Testing
This is the same as external penetration testing but we test for exploits specific to web applications such as SQL injection, cross-site scripting, directory traversal, etc. All work is performed according to the OWASP Top Ten framework.
Security Assessments
We document current practices against a maturity scoring system and provide recommendations towards development and maturity of information security in alignment to your operating environment. This service is good for organizations who are concerned about passing an audit and need an objective review of existing controls prior to an actual audit.
Policy Development
We help organizations write comprehensive policies to address today’s unique cybersecurity challenges such as bring-your-own-device (BYOD), incident response, and third-party vendor management.
Security Awareness Training
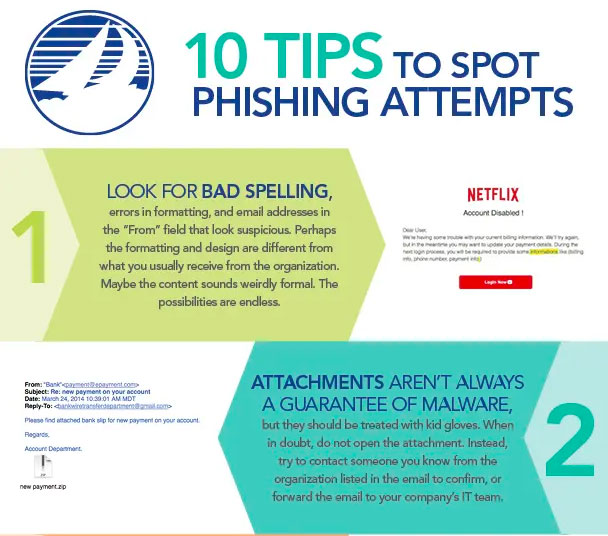
Most malware enters organizations through malicious websites or email attachments. We offer online training modules designed to teach users about best practices when handling email, using mobile devices, working in public spaces, and dealing with social engineering attacks.
Great Lakes Can Support Organizations Under Ohio’s Data Protection Act (ODPA)
Ohio Senate Bill 220, known as the Ohio Data Protection Act, has been signed into law. Organizations of every size have an opportunity to limit liability in the case of a data breach. To meet the requirements for safe harbor, the organization must demonstrate compliance with the National Institute of Standards and Technology (NIST) Cybersecurity Framework. The NIST Cybersecurity Framework is a voluntary framework that provides organizations with standards, guidelines, and best practices to better manage cybersecurity-related risk.
The Ohio Data Protection Act states that if an organization implements and maintains a cybersecurity program that complies with one of the established cybersecurity frameworks (NIST, HIPAA, GLBA, etc.), then that organization “is entitled to an affirmative defense to any cause of action sounding in tort that is brought under the laws of this state or in the courts of this state and that alleges that the failure to implement reasonable information security controls resulted in a data breach concerning personal information.”

According to the Act, to qualify for safe harbor, the organization must:
1. Create, maintain, and comply with a written cybersecurity program that contains administrative, technical, and physical safeguards for the protection of personal information and that reasonably conforms to an industry recognized cybersecurity framework; or
2. Create, maintain, and comply with a written cybersecurity program that contains administrative, technical, and physical safeguards for the protection of both personal information and restricted information and that reasonably conforms to an industry recognized cybersecurity framework.
Great Lakes Computer Corporation provides organizations with cybersecurity consulting services to achieve compliance with NIST SP800-171. We coach companies on how to protect their data and assets.

Why did we choose Cyberstone?
They offer a comprehensive suite of security and compliance services to help end users combat hackers and meet regulatory compliance demands. They provide a valuable tool set that complements Great Lakes Computers’ services and enables us to give our clients a robust approach to security.