Digital Risk Webinar
webinar
Digital Risk: Protecting Your Most Important Asset

Data breaches are a real threat that should be taken seriously, and SMBs have a higher susceptibility of suffering a breach. It’s important to understand the potential threats, how they can affect your business, and what you can do to reduce the risks.
At Great Lakes Computer, we are focused on your company’s security, ensuring that your assets are protected. To help keep you informed of potential threats and how we’re meeting them head on, I would like to invite you to learn more during our pre-recorded webinar, “Digital Risk: Protecting Your Most Important Asset,” which will take a close look at how your business credentials end up for sale on the Dark Web and what can be done to monitor and detect when your organization is at risk.
Viewers are eligible to receive a FREE Dark Web Scan of their network that will give you visibility on your exposed credentials – emails, passwords, etc. – available on the dark web. Then we can help you address the vulnerabilities.
To view the 45-minute webinar, please submit the form and we will send you the link. Thank you for your interest and stay safe!
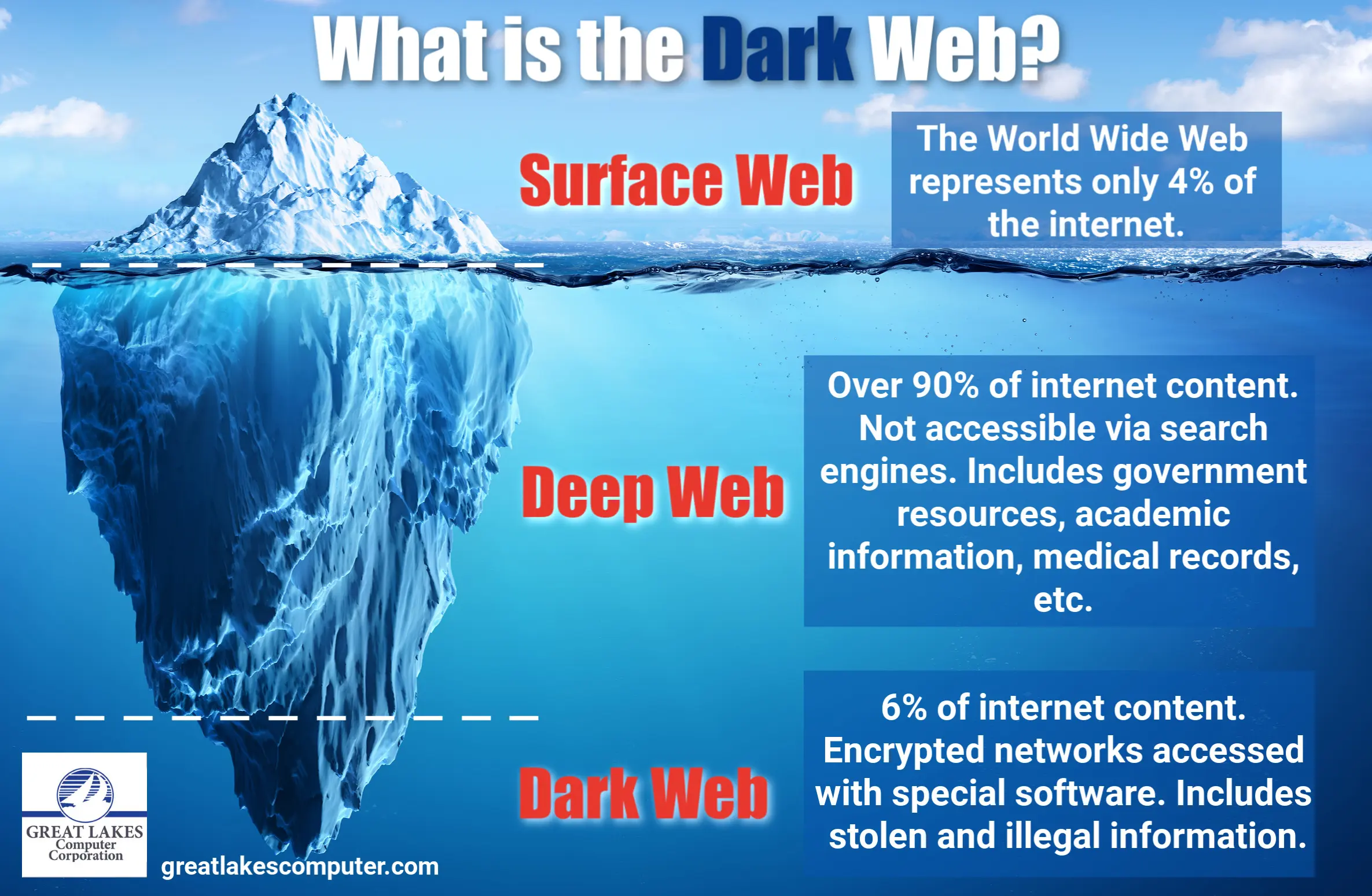
What is the Dark Web?
The Dark Web is a network of websites, forums, and communication tools like email. Users are required to run a suite of security tools that help anonymize web traffic. The Dark Web is used for both nefarious and reputable purposes. Criminals exploit the network’s anonymity to sell guns, drugs, and humans, while organizations like the UN and Facebook use encryption to protect dissidents in oppressive countries.
Who does the Dark Web affect?
Every internet user. If your data was leaked as part of a government or corporate hack, it’s for sale on the Dark Web.
What does the Great Lakes Computer Dark Web ID scan do?
We give small businesses the same visibility into their exposed credentials – emails, passwords, etc. – on the dark web as an enterprise-sized entity or large corporation. Then we help you address the vulnerabilities. Learn about our data security services here.
The next step, if needed, is to provide around the clock alerting and monitoring for signs of compromised credentials, constantly scouring millions of sources including botnets, criminal chat rooms, peer-to-peer networks, malicious websites and blogs, bulletin boards, illegal black-market sites; and other private and public forums.

